UAC-0247 Targets Ukrainian Clinics and Government in Data-Theft Malware Campaign
UAC-0247 كاتستهدف سبيطارات ومؤسسات حكومية ف أوكرانيا ف حملة ديال سرقة البيانات
UAC-0247 Targets Ukrainian Clinics and Government in Data-Theft Malware Campaign
TL;DR
The Computer Emergencies Response Team of Ukraine (CERT-UA) has identified a new cyberattack campaign by threat group UAC-0247. Active between March and April 2026, the group uses phishing emails detailing humanitarian aid to infect systems at healthcare and government institutions. The campaign utilizes multi-stage loaders to deploy "AGINGFLY" and "RAVENSHELL" malware, ultimately stealing sensitive data from WhatsApp and Chromium-based browsers.
The Computer Emergencies Response Team of Ukraine (CERT-UA) recently disclosed details regarding a sophisticated cyber campaign targeting municipal healthcare institutions—specifically clinics and emergency hospitals—as well as government bodies and the Defense Forces of Ukraine.
Attributed to a threat cluster tracked as UAC-0247, the operations observed between March and April 2026 aim to exfiltrate sensitive credentials and communication data. While the activity is well-documented, the specific origins of UAC-0247 remain unknown at this time.
The Infection Vector: Humanitarian Aid Deception
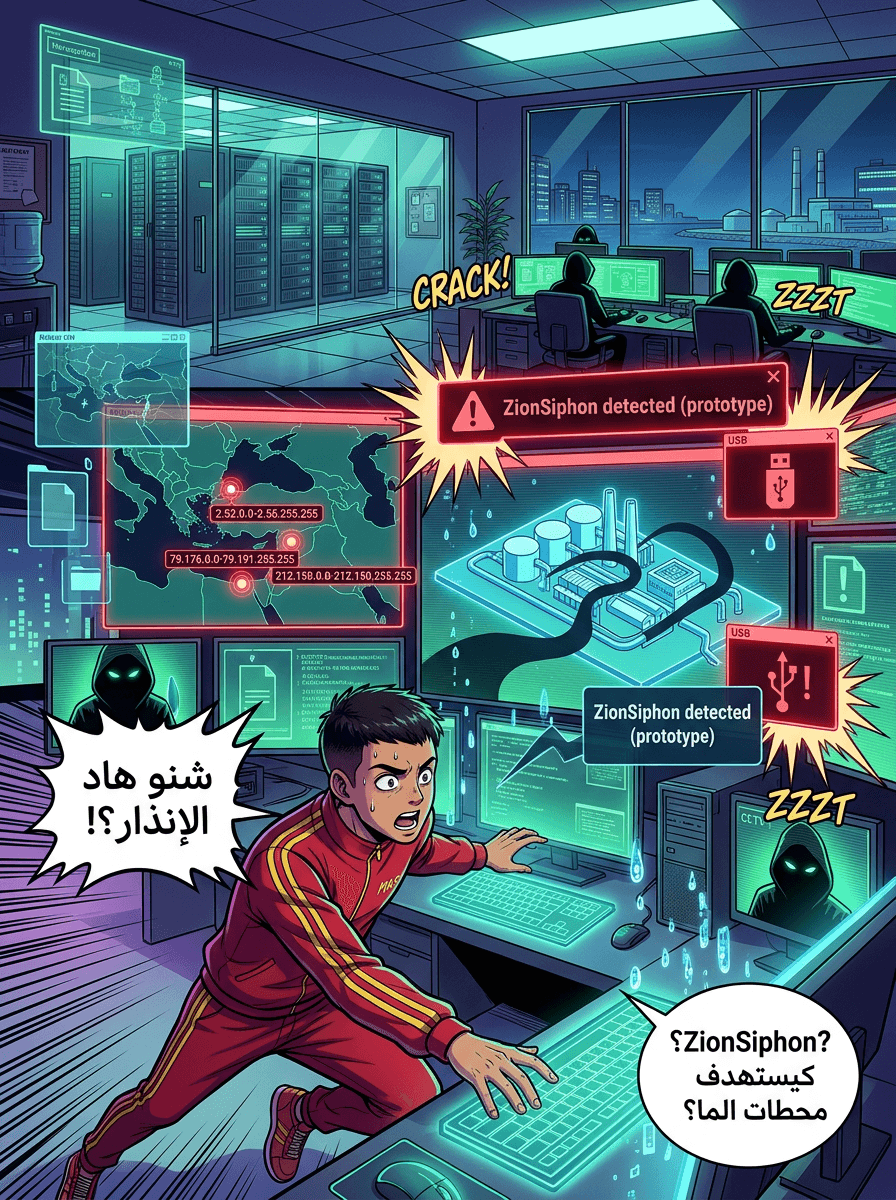
The attack chain typically begins with a phishing email. These messages are themed around "humanitarian aid proposals" to exploit the current socio-political climate in Ukraine.
Recipients are urged to click a link that leads to one of two destinations:
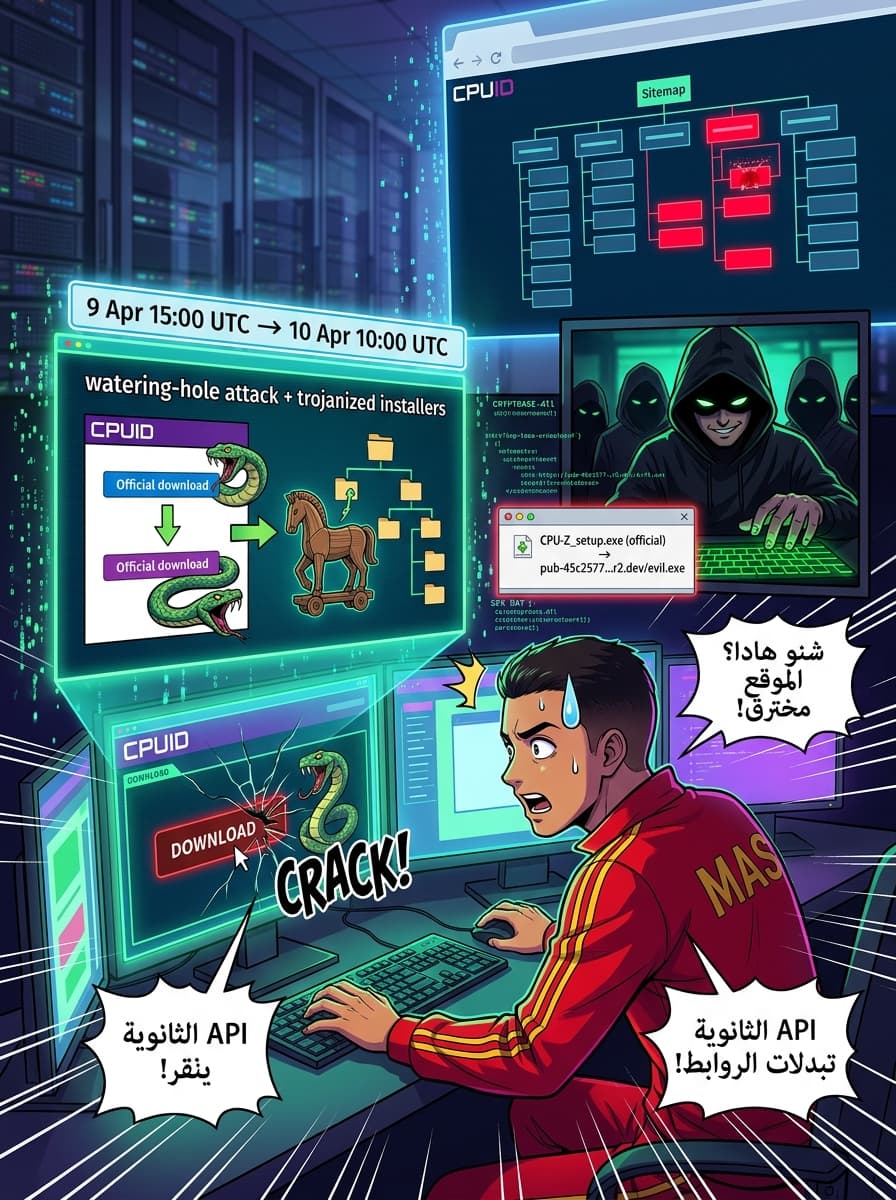
- A Compromised Legitimate Site: Victims are redirected to a real website that has been compromised via a cross-site scripting (XSS) vulnerability.
- AI-Generated Fraudulent Sites: Victims are sent to a bogus website created with the assistance of artificial intelligence (AI) tools.
The goal of these landing pages is to trick the user into downloading and running a Windows Shortcut (LNK) file.
Technical Analysis of the Attack Chain
Once the LNK file is executed, it triggers a multi-stage infection process:
- Initial Execution: The LNK file executes a remote HTML Application (HTA) using the native Windows utility
mshta.exe. - Diversion and Injection: While the HTA displays a decoy form to distract the victim, it silently fetches a binary. This binary injects shellcode into a legitimate process, such as
runtimeBroker.exe. - Sophisticated Loaders: CERT-UA noted the use of a two-stage loader. The second stage utilizes a proprietary executable format supporting code and data sections, function imports, and relocation. The final payload is both encrypted and compressed to evade detection.
The Malware Arsenal: RAVENSHELL and AGINGFLY
The campaign deploys several proprietary and specialized tools to maintain control over infected hosts:
- RAVENSHELL: A TCP reverse shell tool that establishes a connection with a management server, allowing attackers to execute commands via
cmd.exe. - SILENTLOOP: A PowerShell script designed to execute commands and auto-update configurations. Notably, it can obtain Command-and-Control (C2) server addresses from a Telegram channel, with built-in fallback mechanisms.
- AGINGFLY: Written in C#, this is the primary remote control tool. It uses WebSockets to communicate with the C2 server, enabling attackers to log keystrokes, download additional files, and execute further payloads.
Data Exfiltration and Lateral Movement
The primary objective of UAC-0247 appears to be reconnaissance and the theft of sensitive information. CERT-UA identified the use of several open-source tools within the compromised networks, including:
- ChromElevator: Used to bypass Chromium’s App-Bound Encryption (ABE) to steal passwords and cookies.
- ZAPiXDESK: A forensic tool used to decrypt local WhatsApp Web databases.
- RustScan & Ligolo-Ng: Used for network scanning and establishing tunnels for lateral movement.
- Chisel: Used for network traffic tunneling.
- XMRig: A cryptocurrency miner, suggesting the attackers also seek to monetize infected hardware.
Evidence of Military Targeting
While healthcare institutions were the primary focus, CERT-UA found evidence that the Defense Forces of Ukraine were also targeted. In these instances, malicious ZIP archives were distributed via the Signal messaging app, using DLL side-loading techniques to drop the AGINGFLY malware.
Conclusion and Mitigation
The UAC-0247 campaign demonstrates a high level of agility, combining social engineering with sophisticated proprietary loaders and open-source forensic tools. To defend against these threats, CERT-UA recommends that organizations restrict the execution of specific file types and utilities.
Recommended Defensive Measures:
- Restrict the execution of LNK, HTA, and JS files.
- Monitor or restrict high-risk legitimate Windows utilities, including
mshta.exe,powershell.exe, andwscript.exe.
Source: The Hacker News - UAC-0247 Targets Ukrainian Clinics and Government in Data-Theft Malware Campaign