PyTorch Lightning and Intercom-client Hit in Supply Chain Attacks to Steal Credentials
رد بالكم: هجمة Supply Chain ضربات PyTorch Lightning و Intercom
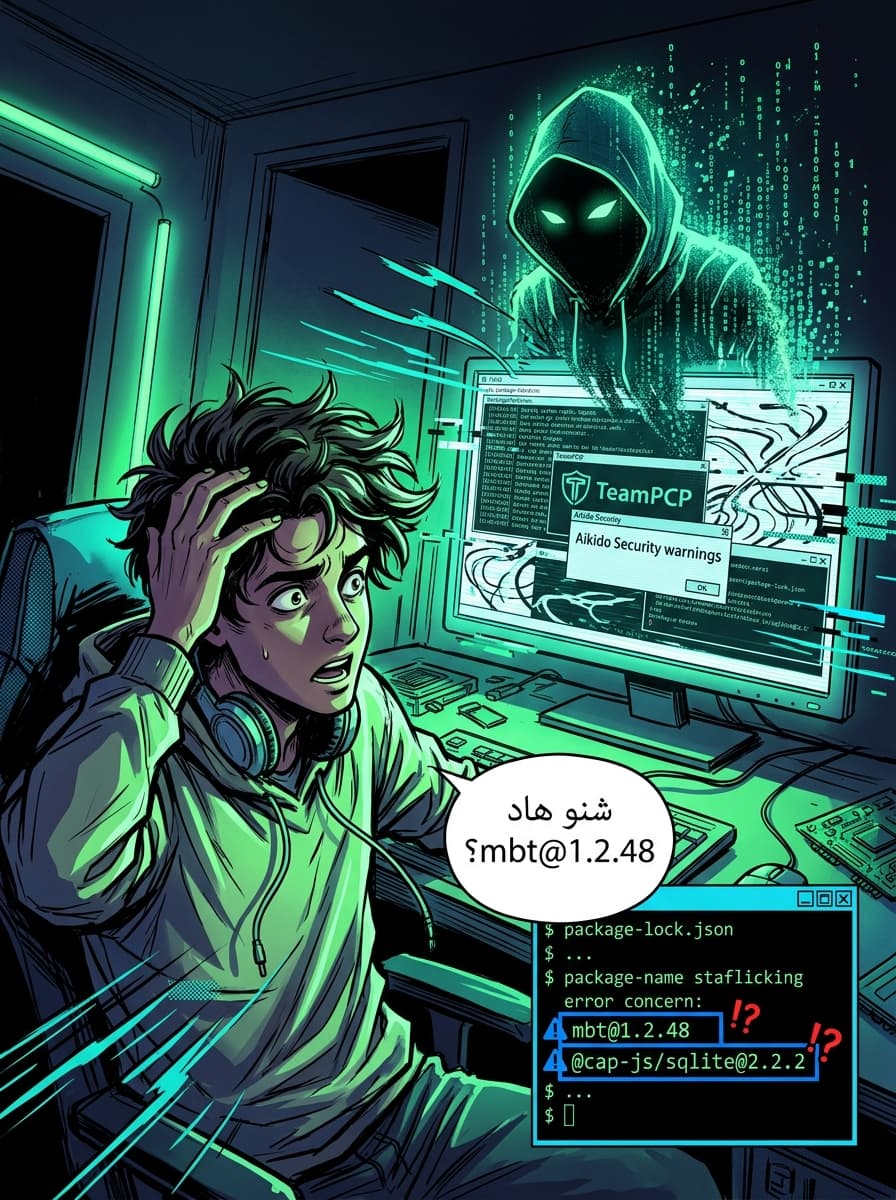
TeamPCP Compromises PyTorch Lightning and Intercom Packages in Widespread Supply Chain Attack
TL;DR
The popular Python framework PyTorch Lightning and the Intercom client libraries were recently hit by a sophisticated supply chain attack orchestrated by the threat actor TeamPCP. Malicious versions were published on April 30, 2026, designed to steal sensitive credentials and propagate via GitHub and npm. If you use these tools, you must immediately downgrade and rotate all environment secrets, including GitHub tokens and SSH keys.
The Anatomy of the Attack: Lightning Under Fire
On April 30, 2026, the Python Package Index (PyPI) saw the release of two compromised versions of Lightning (the high-level interface for PyTorch): 2.6.2 and 2.6.3. These versions were modified to include a hidden _runtime directory containing a downloader and an obfuscated JavaScript payload.
According to security researchers from Socket, Aikido Security, and OX Security, the malware executes automatically the moment the lightning module is imported. For Moroccan developers working on AI and Machine Learning models, this means the infection occurs during standard development workflows, requiring no manual execution of suspicious files.
The execution chain follows a specific path:
- A Python script called
start.pydownloads the Bun JavaScript runtime (a fast JavaScript all-in-one toolkit). - Bun is used to run an 11MB obfuscated payload named
router_runtime.js. - The payload scans for credentials, targeting GitHub tokens, SSH keys, Cloud credentials, Kubernetes configurations, and
.envfiles.
Global Propagation: The "Mini Shai-Hulud" Campaign
This incident is not an isolated event. It is part of a larger campaign dubbed "Mini Shai-Hulud," attributed to the threat group TeamPCP. The group, which claims a partnership with the notorious LAPSUS$ collective, has been targeting various ecosystems, including SAP-related npm packages.
The attack uses a "worm-like" mechanism to spread. Once a developer's GitHub token is stolen, the malware validates it and attempts to inject malicious code into up to 50 branches of every repository the token has write access to. To mask its activity, the poisoned commits impersonate Anthropic's Claude Code identity.
Transitive Dependencies: How Intercom was Reached
One of the most concerning aspects of this campaign is how it jumps between ecosystems. The Intercom-client (npm version 7.0.4) and intercom-php (Packagist version 5.0.2) were also compromised.
Investigations by Intercom revealed that their compromise was a downstream effect. A local installation of the package pyannote-audio introduced the compromised Lightning package as a transitive dependency. A transitive dependency is a library that is not installed by the developer directly, but is required by another package that was installed. This demonstrates how a single vulnerability in the Python ecosystem can bridge into JavaScript and PHP environments.
Technical Analysis of the Stealer
The malware is designed for comprehensive data exfiltration. If it successfully harvests credentials, it attempts to send them to a remote server (zero.masscan[.]cloud). If that fails, it uses a fallback method: it creates a public GitHub repository using the stolen token, with the description "A Mini Shai-Hulud has Appeared," and uploads the stolen data there.
Key Technical Terms:
- Supply Chain Attack: An attack that targets a third-party software provider to reach their customers (e.g., poisoning a library on PyPI).
- Postinstall/Preinstall Hooks: Scripts in a package configuration (like
package.json) that run automatically when a user installs a library. - Transitive Dependency: When Package A relies on Package B, and Package B relies on Package C, Package C is a transitive dependency of Package A.
Evidence and Attestation
While the exact method of the initial compromise at Lightning remains unclear, maintainers suspect a compromise of the project's GitHub account. TeamPCP has been active on the dark web via an onion site, where they have claimed ownership of a "private locker" called CipherForce and denied the use of VECT encryption tools.
The PyPI administrators briefly quarantined the Lightning project to prevent further infections, but the quarantine has since been lifted following the removal of the malicious versions.
Required Actions for Moroccan Teams
If you or your team have installed or updated Lightning or Intercom packages between April 30, 2026, and today, you must take the following steps immediately:
- Remove Malicious Versions: Delete Lightning versions 2.6.2 and 2.6.3.
- Downgrade: Revert to the last known safe version, which is 2.6.1.
- Clean Other Ecosystems: Ensure you are not using
intercom-client(npm) version 7.0.4 orintercom/intercom-php(Packagist) version 5.0.2. - Credential Rotation (Critical): Because the malware targets high-value secrets, you must rotate:
- GitHub Personal Access Tokens (PATs) and SSH keys.
- NPM and PyPI publish tokens.
- Cloud provider keys (AWS, Azure, GCP).
- Kubernetes and Vault secrets.
- Audit Repositories: Check your GitHub branches for unauthorized commits, especially those appearing to come from "Claude Code."
Conclusion
The "Mini Shai-Hulud" campaign highlights a sophisticated shift in supply chain attacks, where threat actors use one compromised ecosystem as a launching pad for others. For the Moroccan tech community—where Python and JavaScript are staples of the local outsourcing and startup scenes—this serves as a reminder that security does not end at your own code. It extends through every dependency in your requirements.txt or package.json.
Source: The Hacker News - PyTorch Lightning and Intercom-client Hit in Supply Chain Attacks