[Webinar] Eliminate Ghost Identities Before They Expose Your Enterprise Data
l-Xatar l-Sakat: Kifach t-Hiyed "l-Huwiyat l-Chabah" (Ghost Identities) Qbeil may-Fdh'u l-Data dyal l-Charika dyalk
The Silent Threat: Eliminating Ghost Identities Before They Expose Your Enterprise Data
TL;DR
In 2024, 68% of cloud breaches were caused by compromised service accounts and forgotten API keys—outpacing phishing and weak passwords. These "Ghost Identities" outnumber human employees 45-to-1 and often carry excessive privileges. Learn how to secure your non-human identity (NHI) perimeter before attackers exploit these unmonitored back doors.
The New Frontier of Cloud Breaches
For years, cybersecurity training has focused on the "human element"—warning employees about phishing emails and enforcing strong password policies. However, recent data suggests the real danger lies elsewhere.
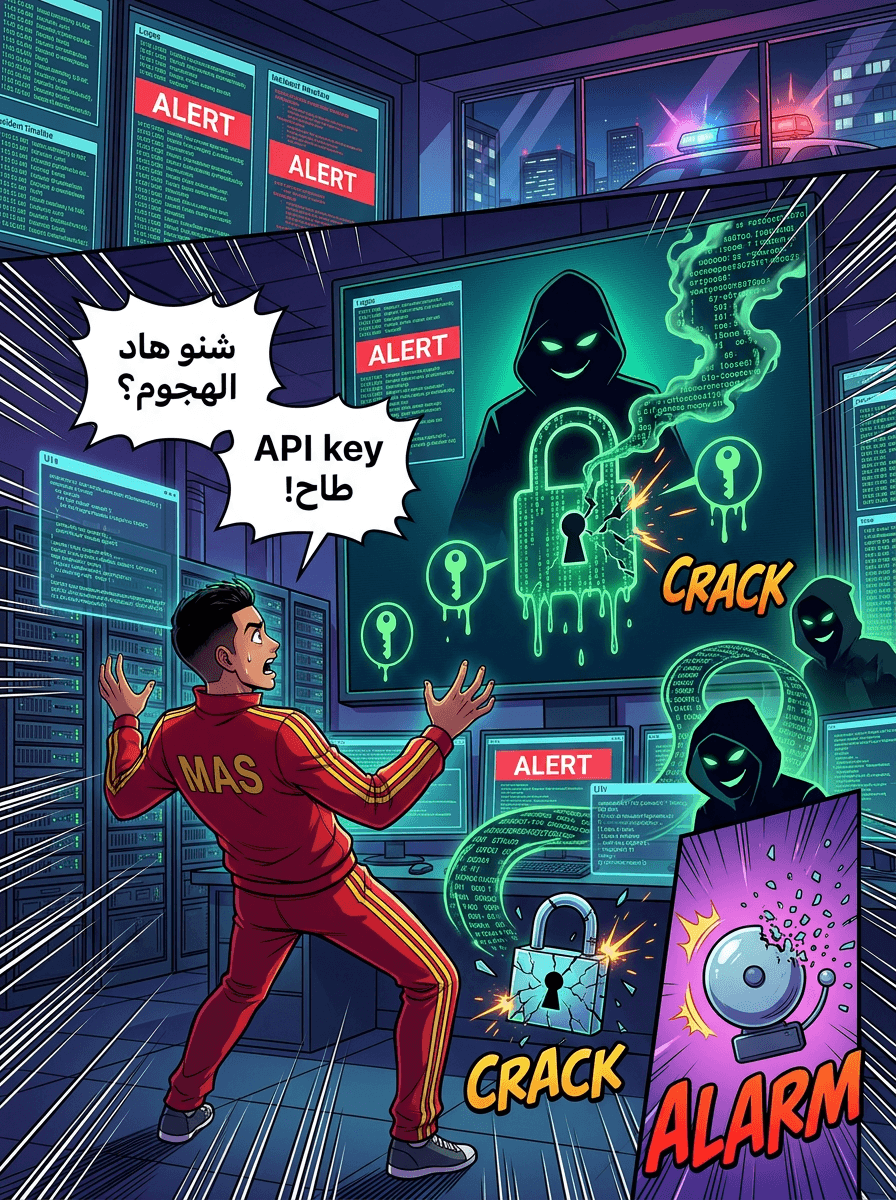
In 2024, 68% of cloud breaches were attributed to compromised service accounts and forgotten API keys. These are not human errors in the traditional sense; they are failures in managing Non-Human Identities (NHIs). While security teams focus on user logins, attackers are increasingly choosing the path of least resistance: picking up the "keys" left out in the open.
The Rise of the machines: 45-to-1
The scale of the non-human identity Problem is staggering. In a typical modern enterprise, for every single human employee, there are between 40 to 50 automated credentials. These include:
- Service accounts
- API tokens
- AI agent connections
- OAuth grants
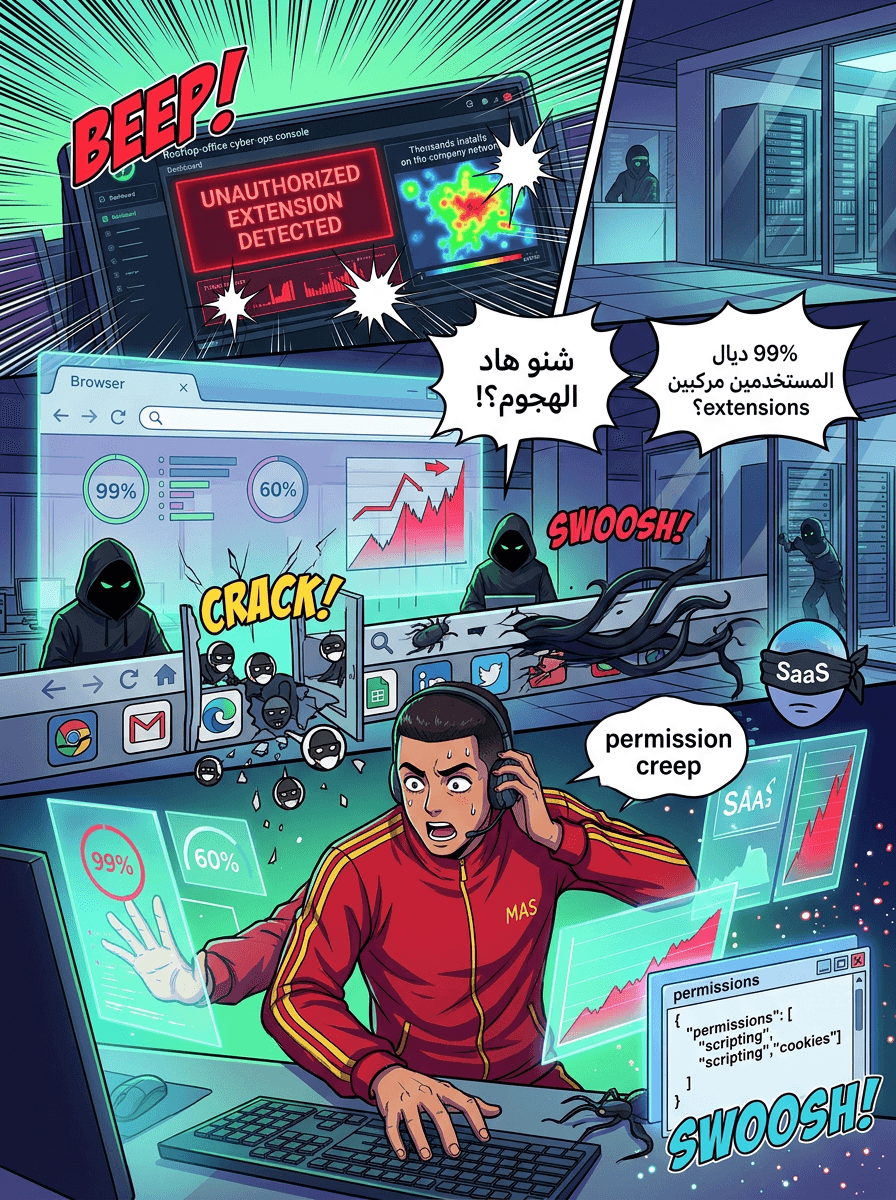
As AI agents and automated workflows multiply, these credentials are being created at a pace that manual security tracking cannot sustain.
What are "Ghost Identities"?
A Ghost Identity is an automated credential that remains active long after its purpose has served. When a specific project ends or a developer leaves the company, the human access is revoked, but the service accounts and API tokens created during that period often stay active, fully privileged, and completely unmonitored.
These "ghosts" are particularly dangerous because:
- Over-Privilege: Many carry admin-level access they never actually required.
- Lateral Movement: A single compromised token can allow an attacker to move laterally across an entire cloud environment.
- Extended Dwell Time: Because traditional Identity and Access Management (IAM) tools focus on people rather than machines, these intrusions often go unnoticed. The average dwell time for these types of breaches currently exceeds 200 days.
Why Traditional IAM Falls Short
Traditional IAM solutions were built with a "human-centric" design. They are effective at managing employee lifecycles—onboarding, role changes, and offboarding. However, they struggle to gain visibility into the machine layer. They ignore the secret keys embedded in code, the tokens used by background processes, and the integrations connecting various SaaS platforms.
Building a Playbook for Non-Human Identity Security
To combat this growing threat, security teams must move beyond manual tracking and adopt a structured framework for identity cleanup. To address this, an upcoming webinar will provide a working playbook for securing your environment, focusing on:
- Discovery: Running full scans to identify every non-human identity within the environment.
- Permission Right-Sizing: Implementing a framework to ensure service accounts and AI integrations have only the permissions necessary for their tasks.
- Automated Lifecycle Policies: Establishing rules so that "dead" or inactive credentials are automatically revoked before they can be discovered by malicious actors.
Conclusion
The rapid shift to automated workflows and AI integration has created a massive, unmanaged shadow perimeter. As ghost identities continue to outnumber human users, the focus of enterprise security must shift to include the machine layer. Without a proactive strategy to find and eliminate these hidden keys, they remain a wide-open back door for attackers.
Event Information
If you are ready to secure your non-human identities, join the upcoming live session to receive a "Identity Cleanup Checklist" and a step-by-step walkthrough of these security strategies.
Source: Eliminate Ghost Identities Before They Expose Your Enterprise Data
![[Webinar] Mythos Reality Check: Beating Automated Exploitation at AI Speed](/_next/image?url=https%3A%2F%2Fthehackernewsbdarija.com%2Fcdn%2Fhn-generated%2F2026-04-24%2Fwebinar-mythos-reality-check-beating-automated-exploitation-at-ai-speed%2Fmanga_page_1.png&w=3840&q=75)