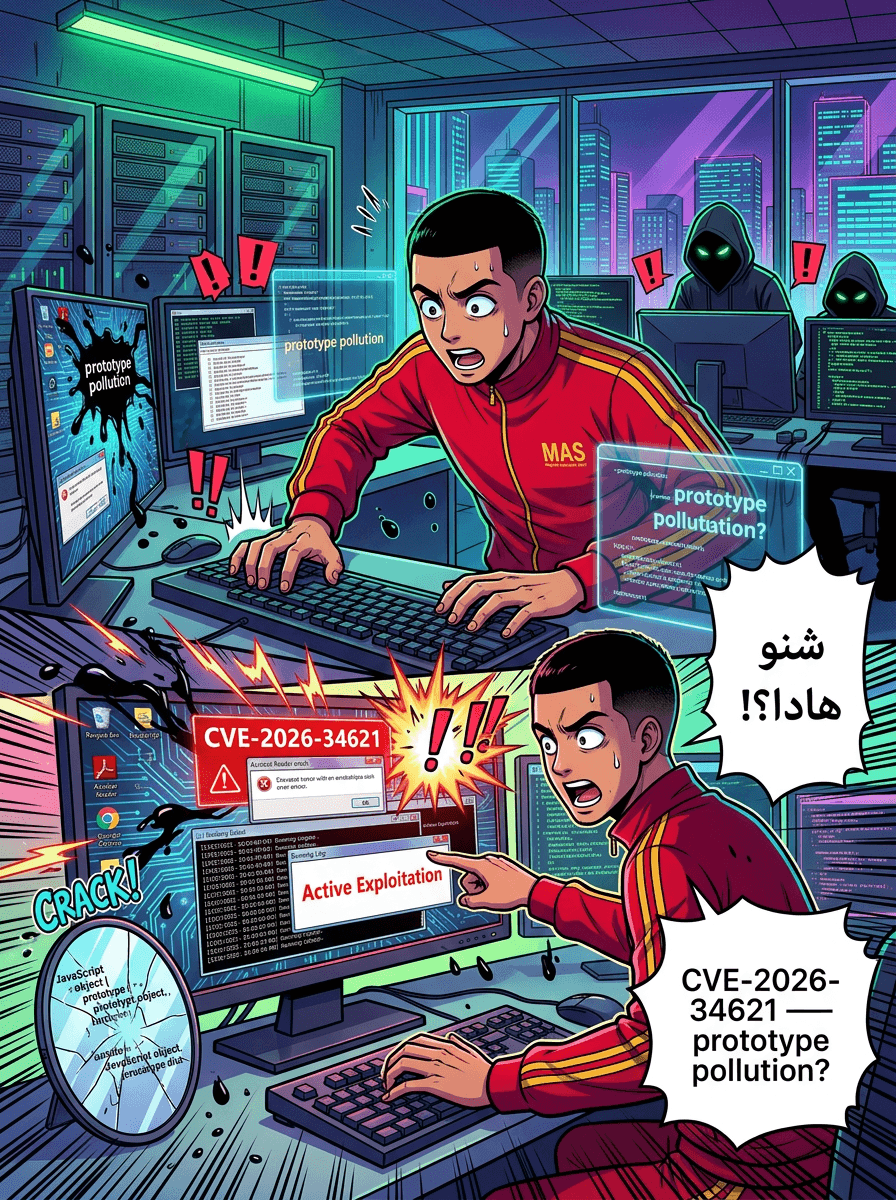
Three Microsoft Defender Zero-Days Actively Exploited; Two Still Unpatched
إنذار بالتصعيد: تلاتة ديال الثغرات "Zero-Day" فـ Microsoft Defender تحت هجوم مستمر
Escalation Alert: Three Microsoft Defender Zero-Days Under Active Attack
TL;DR
Threat actors are actively exploiting three zero-day vulnerabilities in Microsoft Defender to elevate privileges and disable security updates. While Microsoft has patched one flaw (BlueHammer/CVE-2026-33825), two others—RedSun and UnDefend—remain unpatched and are being used in "hands-on-keyboard" attacks.
The security community is on high alert as Huntress reports active exploitation of three recently disclosed vulnerabilities targeting Microsoft Defender. The flaws, originally released as zero-days by a researcher known as Chaotic Eclipse (or Nightmare-Eclipse), were reportedly made public in protest of how Microsoft managed the initial disclosure process.
These vulnerabilities represent a significant risk, as they target the very security software intended to protect Windows environments.
The Vulnerabilities: BlueHammer, RedSun, and UnDefend
The three exploits serve different purposes in a threat actor's toolkit, ranging from gaining administrative control to blinding security defenses.
1. BlueHammer (CVE-2026-33825)
- Type: Local Privilege Escalation (LPE)
- Status: Patched
- Details: This vulnerability allows an attacker with local access to a system to gain elevated privileges. Microsoft addressed this flaw during the April 2026 Patch Tuesday updates. Huntress noted that this specific exploit has been weaponized in the wild since April 10, 2026.
2. RedSun
- Type: Local Privilege Escalation (LPE)
- Status: Unpatched
- Details: Similar to BlueHammer, RedSun allows for privilege escalation within the compromised system. As of the current writing, no official patch has been released for this flaw.
3. UnDefend
- Type: Denial-of-Service (DoS)
- Status: Unpatched
- Details: UnDefend is particularly dangerous for long-term persistence. It can be used to trigger a denial-of-service condition that effectively blocks Microsoft Defender from receiving definition updates, leaving the system vulnerable to newer malware signatures.
Observed Exploitation in the Wild
Huntress has confirmed seeing all three flaws utilized in real-world attacks. According to the cybersecurity vendor, the exploitation follows a predictable pattern of "hands-on-keyboard" activity.
Threat actors typically begin with enumeration commands to map the local environment, including:
whoami /privcmdkey /listnet group
Following these reconnaissance steps, the attackers deploy the zero-day exploits. While BlueHammer was seen as early as April 10, Proof-of-Concept (PoC) exploits for RedSun and UnDefend were observed in use starting April 16.
Microsoft’s Response
Microsoft has confirmed the fix for BlueHammer via CVE-2026-33825. In a statement regarding the situation, a Microsoft spokesperson emphasized their commitment to investigating security issues and supported the practice of coordinated vulnerability disclosure (CVD).
However, the spokesperson did not provide specific timelines for when the remaining two flaws, RedSun and UnDefend, would receive official security updates.
Recommended Actions
Because two of these vulnerabilities remain unpatched, organizations are advised to:
- Apply Patch Tuesday Updates: Ensure CVE-2026-33825 is patched immediately to remediate the BlueHammer vulnerability.
- Monitor for Enumeration: Use EDR (Endpoint Detection and Response) tools to flag unusual use of
whoami,cmdkey, andnetcommands, which may indicate an attacker is preparing for an escalation attempt. - Isolate Compromised Hosts: If suspicious activity is detected, follow Huntress's lead in isolating affected systems to prevent further post-exploitation movements.
Source: The Hacker News