
Mirax Android RAT: Malware jdid kay-red 220,000 jihaz l-SOCKS5 Proxies 3la triq Meta Ads
Mirax Android RAT: Malware jdid kay-red 220,000 jihaz l-SOCKS5 Proxies 3la triq Meta Ads
TL;DR (L-kholasa)
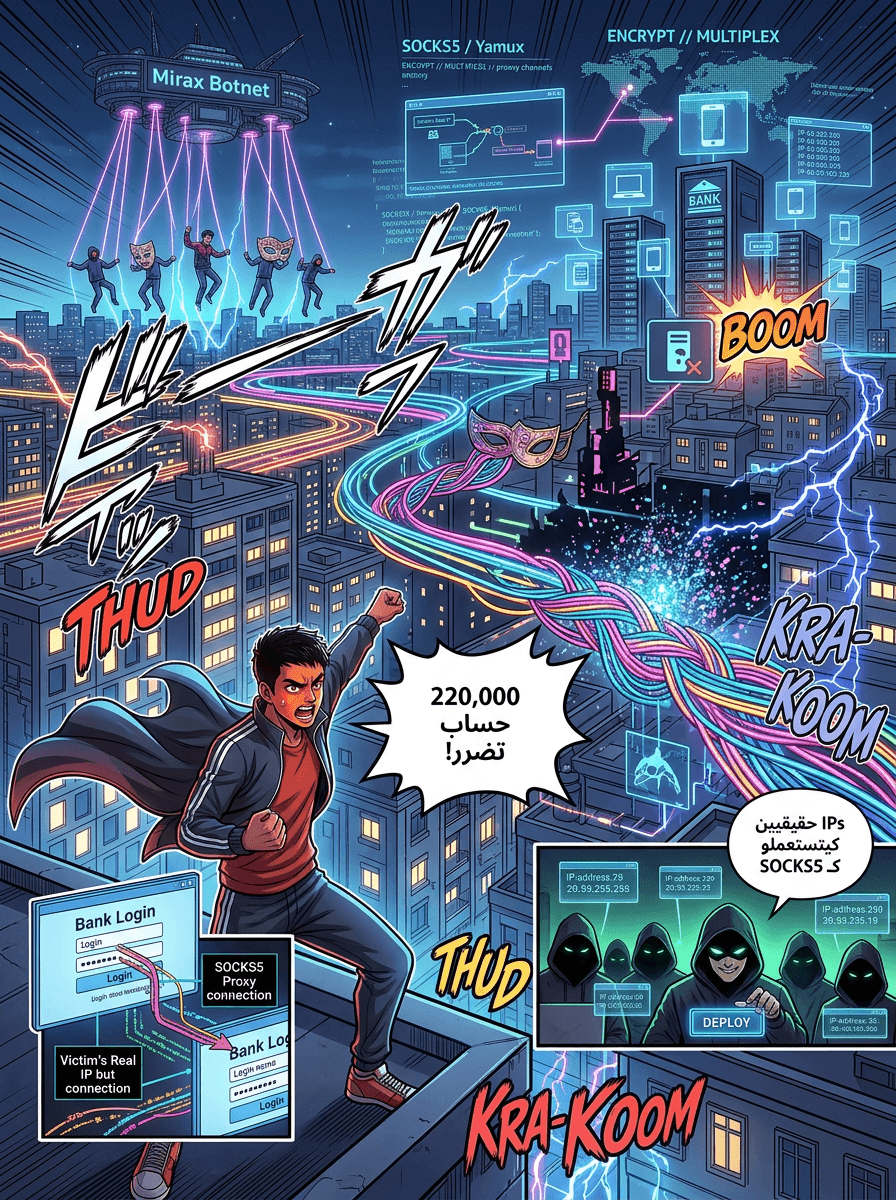
Kayn wahed l-malware jdid dyal l-Android smito Mirax (men naw3 Remote Access Trojan - RAT) kay-it-target l-mostakhdimin li kay-hdrou b-sbanya men khilal ishiharat khadda3a f Facebook u Instagram. Hadi l-malware wslat l-kter men 220,000 hssab, u machi ghir kat-srq l-m3loumat l-khassa dyal nass, walakin kat-red l-hawatif l-mousaba l-node dyal residential SOCKS5 proxy bach t-sa3ed l-hackers ikhbiw l-itir dyalhom u ihrebo men n-didat l-himaya.
Kayn khatar jdid u mtewwer f l-3alam dyal l-mobile. L-bahit l-amniyin f charika l-italiya Cleafy li motakhassissa f l-himaya men l-ihtiyal, ktaf-chfou Mirax, wahed l-Android RAT jdid.
Wakha bezaf dyal l-RATs kay-rkzo ghir 3la l-khitfa dyal l-m3loumat, Mirax m-kh-talef 7it kay-red l-ajhiza li t-sabet l-botnet kbir dyal "residential proxy". B-isti3mal l-IP address l-haqiqiya dyal l-dahia, l-hackers iqdrou idiru 3amaliyat ihtiyaliya u idkhlo l-hssabat l-bankiya u homa m-kh-biyn tmanan 3la n-didat l-moraqaba l-joghrapiya (geolocation).
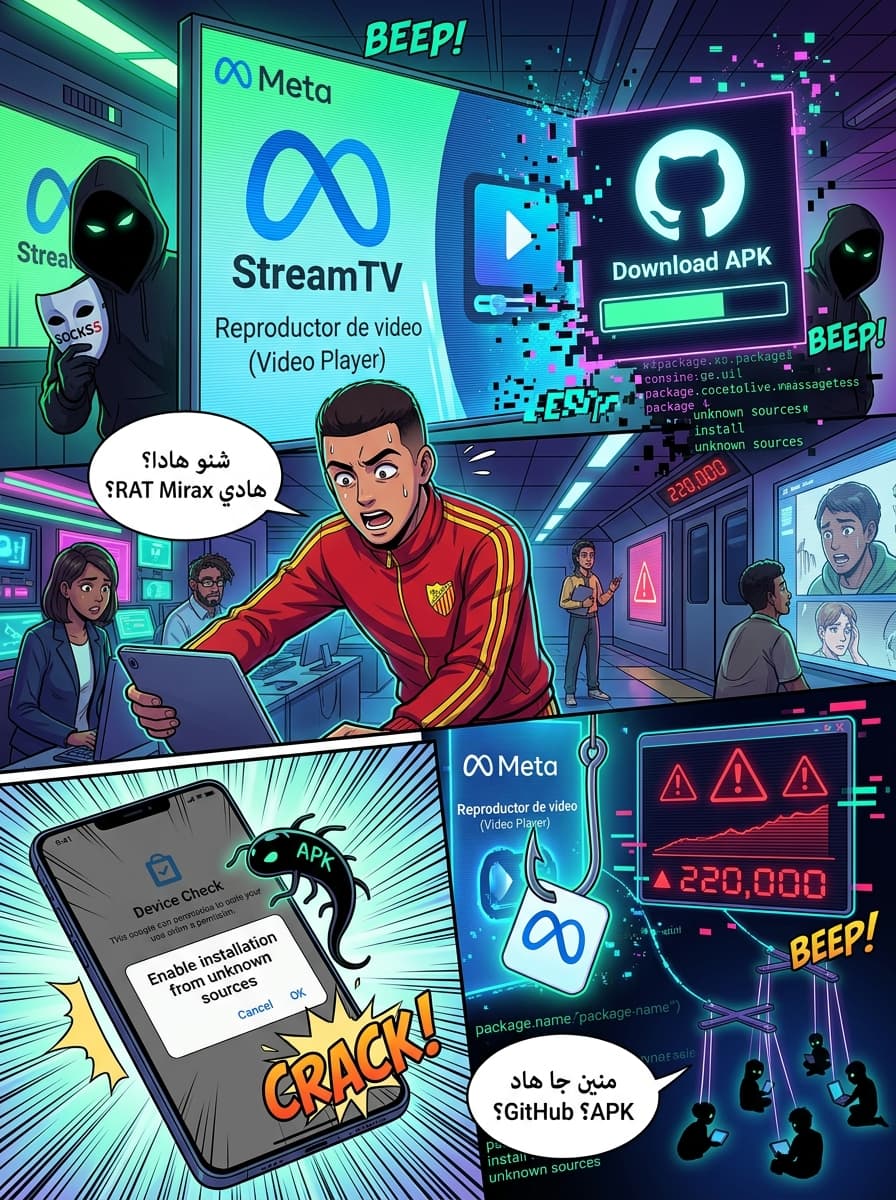
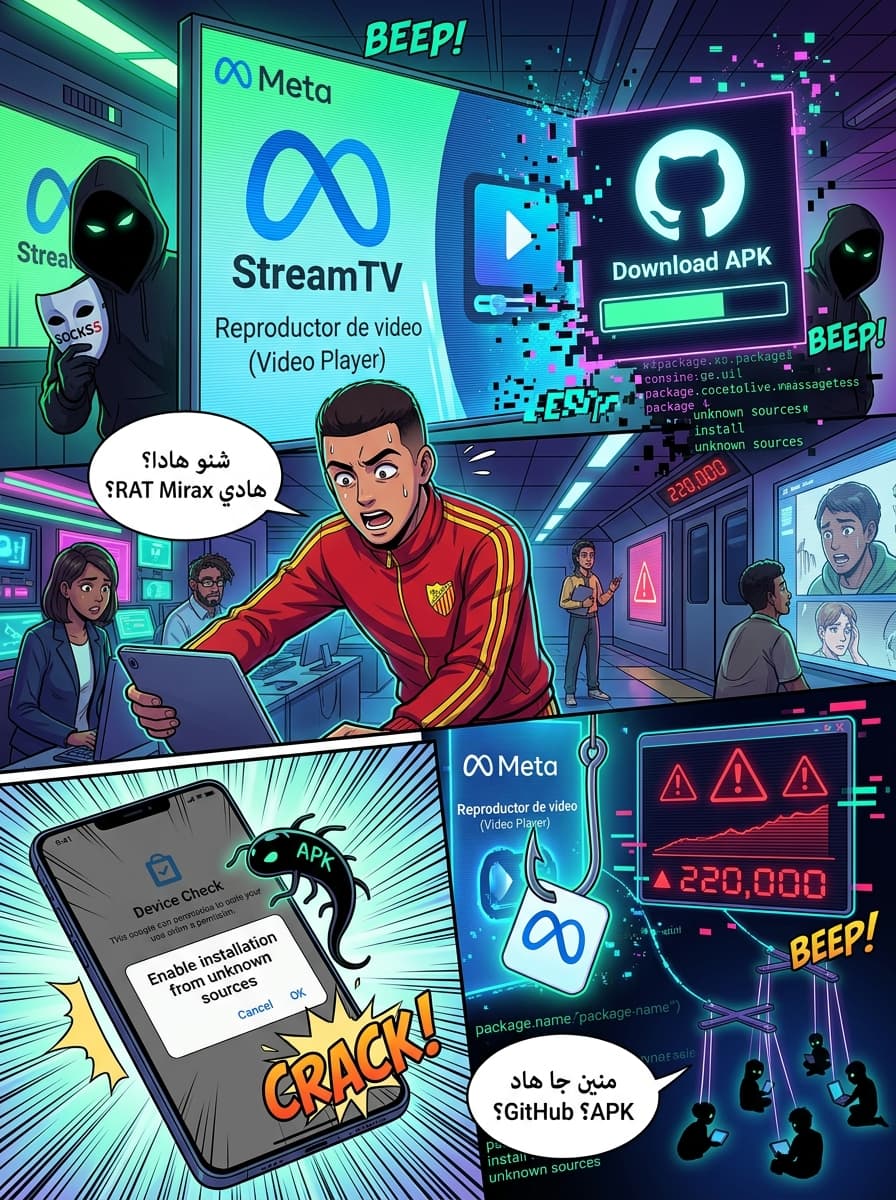
Intichar 3alami 3abr l-ishiharat dyal Meta
L-hamla dyal Mirax wslat l-wahed l-mustawa kbir b-istighlal l-indamat l-ichihariya dyal Meta. L-mohaajimin kanu kay-t-lqo ichiharat f Facebook, Instagram, Messenger, u Threads.
3la hssab l-bahitin, l-hamla wslat l-kter men 220,000 hssab, m-rk-za b-khousous 3la l-boldan li kat-hder b-sbanya. Wahed l-ichihar khass kan kay-روج l-khedma dyal streaming dyal l-koura u l-aflam — u kan khaddam f 6 April 2026 — dkhlo lih lihoudo 191,000 mostakhdim.
Triq bach kay-tm l-houjoum hiya hadi:
- Malicious Ads: Mostakhdimin kay-choufou ads dyal "StreamTV" aw "Reproductor de video" li kay-wa3dou b-aflam u koura fabor.
- Landing Pages Khadda3a: L-ads kay-dikhlo l-websites kay-diro "device check" bach it-akkdu beli l-visitour m-dakhil men portable, had l-khitta bach ihrebo men scan l-amni l-automati.
- GitHub Hosting: L-malware (f-chikl APK) kouno m-hostyin f GitHub bach ibano chri-iin u qanouniyin.
- Social Engineering: Melli kay-t-installa l-dropper, kay-tleb men l-mostakhdim i-autoriser "installation from unknown sources" bach i-deployer l-payload l-khir dyal Mirax.
Kter men RAT 3adi: l-moumizat dyal SOCKS5
Wakha Mirax fih l-moumizat l-3adiya dyal RAT — bhal m-ra-qbat l-klavier (keylogging), sreqt l-tsawer, m-ra-qbat l-chacha, u l-qodra 3la tanfid awamir men b-3id — l-feature l-wa3ra kamla hiya l-integration dyal l-proxy.
B-isti3mal SOCKS5 protocol u Yamux multiplexing, Mirax kay-sawab channels dyal proxy qwiya. Hadchi kay-khali l-operators dyal "Mirax Bot" i-router-iw l-traffic dyalhom l-kha-yib 3abr l-jihaz dyal l-dahia.
3lach hadchi khtir: Melli l-hacker kay-ibghi id-khel l-wahed l-hssab banki m-srouq b-isti3mal l-IP address l-haqiqiya dyal l-dahia, n-didat l-himaya s3ib t-f-yaq biha u kat-3taber l-activity 3adiya.
L-binya t-tiqniya (Technical Infrastructure)
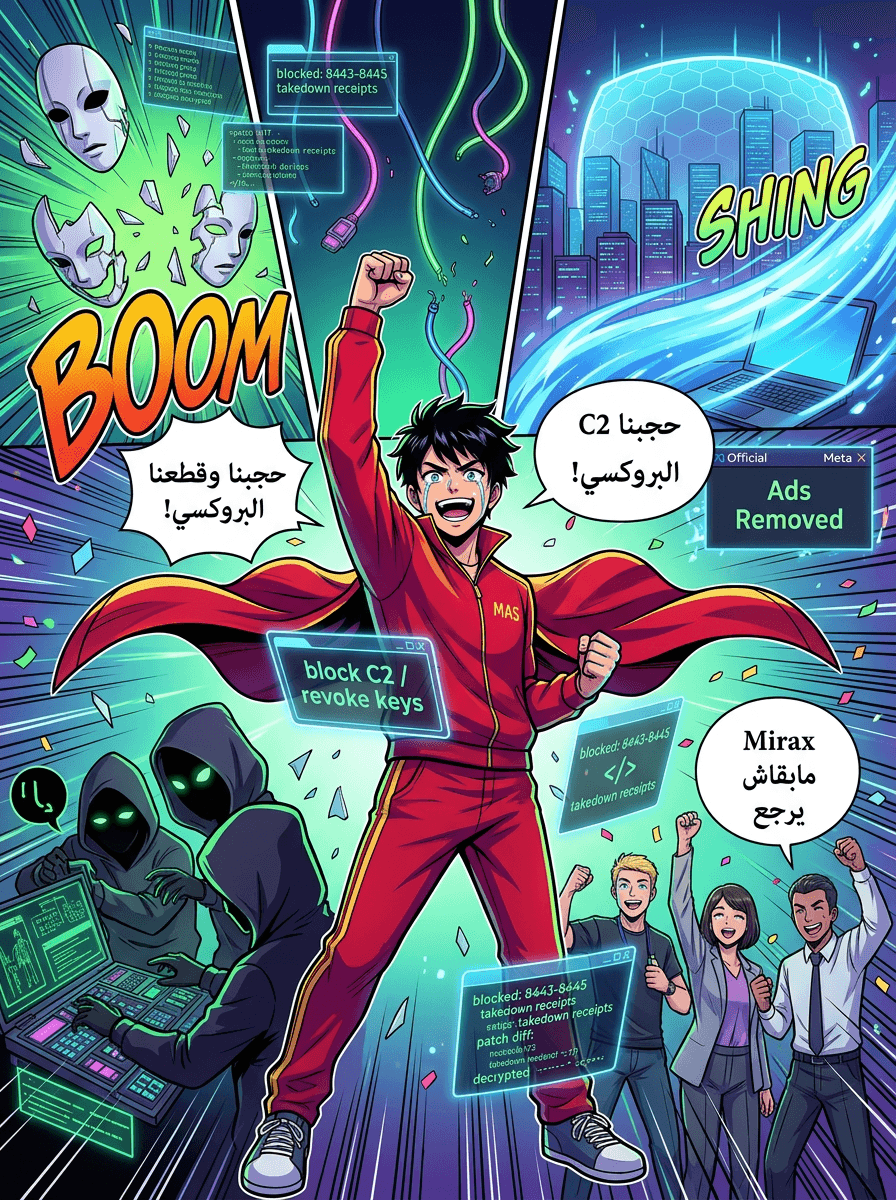
L-malware kay-f-teh tlat dyal l-channels C2 (Command-and-Control) b-istikhdam WebSockets:
- Port 8443: Khass b-remote access u tanfid l-awamir.
- Port 8444: Khass b-remote streaming u s-s-reqt l-data.
- Port 8445: Khass ghi b-s-setup dyal l-residential SOCKS5 proxy.
At-man l-Malware-as-a-Service (MaaS)
Mirax machi ghir adat, rah "business". L-m3loumat l-lowla jlat men KrakenLabs dyal Outpost24, li kta-chfou l-hacker "Mirax Bot" kay-irouej l-had l-malware f l-forums dyal l-underground.
Hadi hiيا l-atman dyal l-ichtirak f had l-khedma:
- Full Suite: $2,500 l-telt chhour.
- Lightweight Variant: $1,750 l-chehar (bla l-moumizat dyal proxy u bla bypass dyal Google Play Protect).
L-bahitin l-ahdou beli l-mowari-in kay-3tiw l-awlawiya l- "affiliates" li kay-hdrou b-rous-siya u 3ndhom som-3a m-zy-ana, hadchi bach i-ha-fdou 3la l-amni dyal l-3amaliyat dyalhom.
L-ihtiyal u l-isti-mrariya (Evasion and Persistence)
Melli kay-t-installa, Mirax kay-it-kh-ba f chikl application dyal video. Kay-bqa is-da3 l-mostakhdim bach i-activer Accessibility Services. Ila k-kh-daha, l-malware iqder:
- I-khdem f l-background bla may-3iq bih hed.
- I-t-la3 "error messages" khadda3a bach l-wahed i-f-iyel beli l-installation f-chelat.
- I-t-la3 HTML overlays (chachat fawqiya) f-wuqt melli l-mostakhdim kay-f-teh app dyal l-banka bach is-raqq lih l-m3loumat.
Bach i-kh-biw l-APKs men l-antivirus, l-Mirax builder kay-khali l-hackers ikh-tarou bin jouj dyal l-"crypters": Virbox aw Golden Crypt, li kay-ch-frou l-code l-khib bach i-h-rebo men Google Play Protect.
Tawajouh jdid f khatar l-mobile
Had l-iktichaf dyal Mirax ja m3a taqarir 3la khatar akhor f l-mintaqa bhal ASO RAT, li huwa malware b-l-3arbiya kay-it-target syriyin b-apps dyal PDF kadi-ba.
Walakin, bahitin dyal Cleafy kay-hederou beli Mirax kiy-metel "marhala jdida". Melli kay-diro l-proxy f wahed l-malware banki kamel, l-hackers mab-qa-uch ghir kay-s-r-qu l-data — raw rad-dou koul tili-foun m-sab tarf men l-binya t-tahtiya dyal l-ij-ram dyalhom.
Source
The Hacker News: Mirax Android RAT Turns Devices into SOCKS5 Proxies